CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right tool.
CMMC ROI
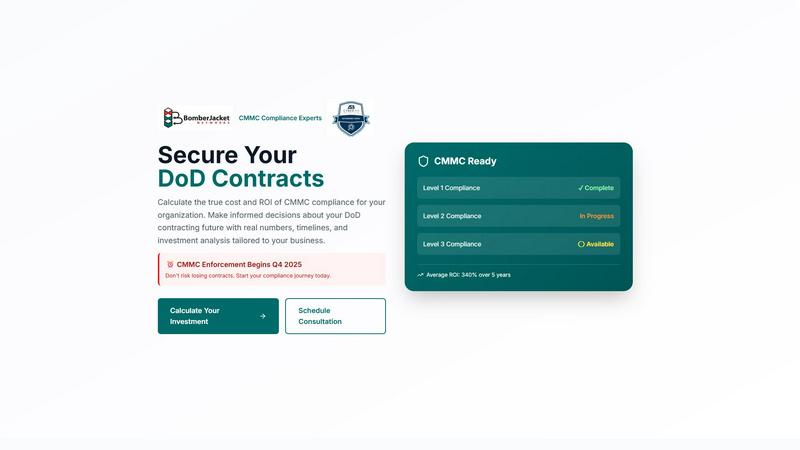
Calculate your CMMC compliance ROI with real data to secure DoD contracts before enforcement begins in 2025.
Last updated: March 1, 2026
Threat Watch
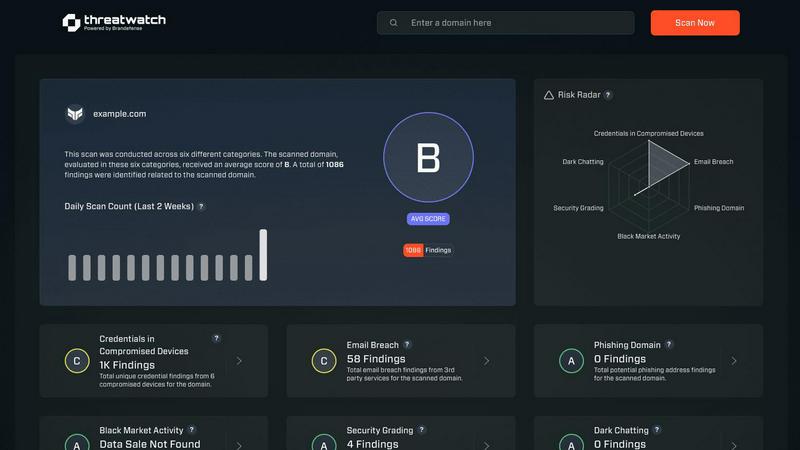
Instantly evaluate your cybersecurity health and identify vulnerabilities to stay ahead of threats with Threat Watch.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Investment Calculator
The CMMC ROI investment calculator allows businesses to input specific parameters, including company size, annual revenue, and CMMC level required. This tool generates a personalized analysis of total investment costs, projected ROI, and payback periods, empowering organizations to make informed financial decisions.
Compliance Progress Tracking
The platform provides a real-time tracking system for compliance status, enabling users to monitor their progression toward CMMC certification. With visual indicators for Level 1, Level 2, and Level 3 compliance, businesses can easily assess their current standing and what steps remain.
Breach Cost Avoidance Analysis
CMMC ROI quantifies the potential financial impact of breaches by calculating the average costs avoided through compliance. Users can see how achieving CMMC certification could protect them from significant financial losses due to breaches and false claims, making it a critical part of their financial strategy.
ROI Projection Timeline
The software features a comprehensive ROI projection timeline that illustrates the break-even point and estimated returns over five years. This timeline helps businesses anticipate when they will recoup their initial investments, facilitating better cash flow management and strategic planning.
Threat Watch
Comprehensive Security Evaluation
Threat Watch conducts a thorough evaluation across multiple security categories, including compromised credentials and dark web contents, providing users with an expansive view of their cybersecurity health.
Real-Time Insights
Equipped with real-time insights, Threat Watch enables organizations to swiftly identify vulnerabilities and exposures, ensuring that they can act immediately to address potential threats.
Automated Assessments
Streamlining the security process, Threat Watch offers automated assessments that reduce the burden on IT teams, allowing them to focus on strategic initiatives rather than manual monitoring.
Dark Web Monitoring
With robust dark web monitoring capabilities, Threat Watch alerts organizations to compromised data and credentials being traded or sold, helping to prevent identity theft and data breaches.
Use Cases
CMMC ROI
Small Contractor Implementation
A small contractor with 1-50 employees can utilize CMMC ROI to understand the financial implications of achieving Level 2 compliance. By analyzing their projected investment and potential ROI, they can confidently navigate their compliance journey and secure valuable contracts.
Medium-Sized Business Strategy
For medium contractors generating $10M in DoD revenue, CMMC ROI provides an in-depth financial analysis that highlights the importance of CMMC compliance. This enables them to make strategic decisions about resource allocation and investment in security measures.
Large Prime Contractor Planning
Large prime contractors can use CMMC ROI to assess their compliance costs and expected returns, especially when facing significant revenue streams from $100M contracts. By outlining the path to Level 3 certification, they can align their compliance efforts with business objectives and protect their market position.
Technology Firm Risk Mitigation
A technology firm in the defense sector can leverage CMMC ROI to evaluate the risks and costs associated with non-compliance. By understanding potential losses due to breaches, they can justify the investment in compliance as a protective measure for their business continuity and reputation.
Threat Watch
Proactive Risk Management
IT security teams can utilize Threat Watch to proactively manage risks by identifying vulnerabilities before they are exploited, thereby preventing costly data breaches and reputational damage.
Compliance and Regulatory Adherence
Compliance officers can leverage Threat Watch to ensure their organization meets regulatory requirements by continuously monitoring for security gaps and addressing them promptly.
Incident Response
In the event of a security incident, organizations can use Threat Watch to quickly assess the situation, identify compromised accounts, and take immediate action to remediate threats.
Executive Reporting
Business leaders can rely on Threat Watch to provide critical data and insights that facilitate informed decision-making regarding cybersecurity investments and strategies, enhancing overall governance.
Overview
About CMMC ROI
CMMC ROI is the premier financial intelligence platform tailored specifically for the defense industrial base, designed to eliminate uncertainty surrounding CMMC compliance costs and benefits. Developed by BomberJacket Networks, an authorized C3PAO and service-disabled veteran-owned business, this platform serves as a strategic investment calculator rather than a mere compliance tool. With the impending enforcement of CMMC regulations set for Q4 2025, DoD contractors face urgent pressure to understand their financial commitments. CMMC ROI provides a comprehensive, data-driven roadmap that clearly outlines your projected five-year investment, estimated payback period, and the potential to achieve a remarkable ROI of over 340%. It's indispensable for business leaders of all sizes—from small FCI contractors to large primes—who need to make informed decisions that safeguard millions in contract revenue, mitigate the risk of costly breaches, and maintain a competitive edge in a rapidly evolving landscape.
About Threat Watch
Threat Watch is an advanced cybersecurity intelligence solution tailored to empower organizations in safeguarding their digital assets. Designed for IT security teams, compliance officers, and business leaders, this tool meticulously evaluates a wide range of critical security categories, including compromised credentials, breached accounts, phishing addresses, and dark web contents. With Threat Watch, organizations gain access to real-time insights and automated assessments that enable them to quickly identify vulnerabilities and exposures. This proactive approach to risk management is essential for protecting sensitive data in today's rapidly evolving cyber landscape. By uncovering critical security issues, Threat Watch equips decision-makers with the information needed to prioritize and mitigate risks effectively, ultimately strengthening the overall cybersecurity posture of the organization. Fast and efficient, Threat Watch allows users to uncover their cybersecurity health in record time, thereby enhancing their defenses against potential threats.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI?
CMMC ROI is a financial intelligence platform designed to help DoD contractors calculate the costs and ROI associated with achieving CMMC compliance. It provides a roadmap that outlines investment, payback periods, and potential returns.
How does the investment calculator work?
The investment calculator allows users to input details about their company size, annual revenue, and required CMMC level. It then generates a tailored analysis of the total investment needed and potential ROI, helping businesses understand their financial commitments.
What are the benefits of achieving CMMC compliance?
Achieving CMMC compliance not only protects contractors from losing contracts but also lowers their risk of financial loss due to breaches. It enhances their credibility and allows them to compete more effectively in the defense contracting landscape.
How is ROI calculated in CMMC ROI?
ROI is calculated using the formula: ROI = (Protected Value - Investment) / Investment × 100. This takes into account the five-year DoD revenue and estimated breach cost avoidance, providing a clear picture of the financial benefits of compliance.
Threat Watch FAQ
How does Threat Watch identify compromised credentials?
Threat Watch employs advanced algorithms and data analysis techniques to scan for compromised credentials across various platforms and databases, providing users with timely alerts.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your cybersecurity framework without disrupting current operations.
What types of organizations benefit the most from Threat Watch?
Organizations of all sizes, from small businesses to large enterprises, can benefit from Threat Watch, particularly those in sectors with stringent security requirements such as finance, healthcare, and e-commerce.
Is Threat Watch suitable for non-technical users?
Absolutely! Threat Watch is user-friendly and designed with non-technical users in mind, providing intuitive interfaces and detailed reports that make cybersecurity accessible to all levels of staff.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a cutting-edge financial intelligence platform tailored for the defense industrial base, designed to provide organizations with critical insights into their CMMC compliance investments. As the DoD prepares to enforce compliance requirements, businesses are increasingly seeking clarity around their financial commitments, prompting many to explore alternatives that may better fit their pricing structures, desired features, or platform capabilities. When evaluating alternatives, users should consider factors such as ease of use, the accuracy of financial projections, the ability to model unique business scenarios, and the overall alignment with their strategic compliance goals.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence solution that falls under the category of business intelligence. It is designed to help organizations evaluate their cybersecurity health by identifying vulnerabilities and providing actionable insights. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, and compatibility with existing platforms. When selecting an alternative, it’s essential to consider the comprehensiveness of risk analysis, the effectiveness of real-time insights, and the quality of automated assessments to ensure robust cybersecurity management.
