Threat Watch
Instantly evaluate your cybersecurity health and identify vulnerabilities to stay ahead of threats with Threat Watch.
About Threat Watch
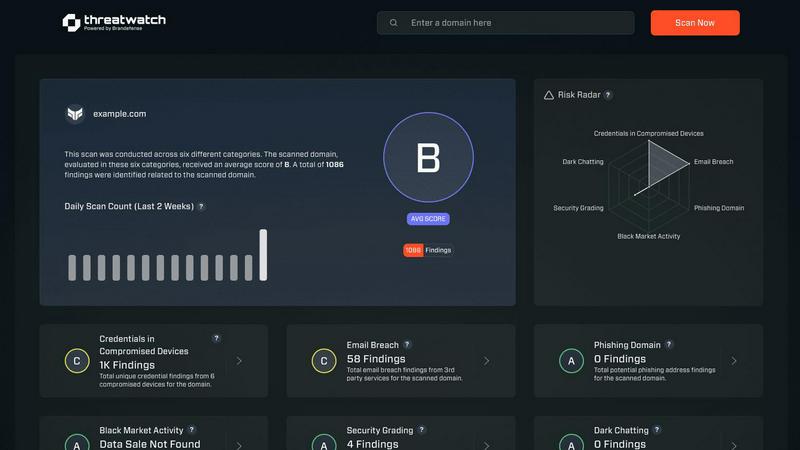
Threat Watch is an advanced cybersecurity intelligence solution tailored to empower organizations in safeguarding their digital assets. Designed for IT security teams, compliance officers, and business leaders, this tool meticulously evaluates a wide range of critical security categories, including compromised credentials, breached accounts, phishing addresses, and dark web contents. With Threat Watch, organizations gain access to real-time insights and automated assessments that enable them to quickly identify vulnerabilities and exposures. This proactive approach to risk management is essential for protecting sensitive data in today's rapidly evolving cyber landscape. By uncovering critical security issues, Threat Watch equips decision-makers with the information needed to prioritize and mitigate risks effectively, ultimately strengthening the overall cybersecurity posture of the organization. Fast and efficient, Threat Watch allows users to uncover their cybersecurity health in record time, thereby enhancing their defenses against potential threats.
Features of Threat Watch
Comprehensive Security Evaluation
Threat Watch conducts a thorough evaluation across multiple security categories, including compromised credentials and dark web contents, providing users with an expansive view of their cybersecurity health.
Real-Time Insights
Equipped with real-time insights, Threat Watch enables organizations to swiftly identify vulnerabilities and exposures, ensuring that they can act immediately to address potential threats.
Automated Assessments
Streamlining the security process, Threat Watch offers automated assessments that reduce the burden on IT teams, allowing them to focus on strategic initiatives rather than manual monitoring.
Dark Web Monitoring
With robust dark web monitoring capabilities, Threat Watch alerts organizations to compromised data and credentials being traded or sold, helping to prevent identity theft and data breaches.
Use Cases of Threat Watch
Proactive Risk Management
IT security teams can utilize Threat Watch to proactively manage risks by identifying vulnerabilities before they are exploited, thereby preventing costly data breaches and reputational damage.
Compliance and Regulatory Adherence
Compliance officers can leverage Threat Watch to ensure their organization meets regulatory requirements by continuously monitoring for security gaps and addressing them promptly.
Incident Response
In the event of a security incident, organizations can use Threat Watch to quickly assess the situation, identify compromised accounts, and take immediate action to remediate threats.
Executive Reporting
Business leaders can rely on Threat Watch to provide critical data and insights that facilitate informed decision-making regarding cybersecurity investments and strategies, enhancing overall governance.
Frequently Asked Questions
How does Threat Watch identify compromised credentials?
Threat Watch employs advanced algorithms and data analysis techniques to scan for compromised credentials across various platforms and databases, providing users with timely alerts.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your cybersecurity framework without disrupting current operations.
What types of organizations benefit the most from Threat Watch?
Organizations of all sizes, from small businesses to large enterprises, can benefit from Threat Watch, particularly those in sectors with stringent security requirements such as finance, healthcare, and e-commerce.
Is Threat Watch suitable for non-technical users?
Absolutely! Threat Watch is user-friendly and designed with non-technical users in mind, providing intuitive interfaces and detailed reports that make cybersecurity accessible to all levels of staff.
Explore more in this category:
Similar to Threat Watch
FX Radar
FX Radar delivers real-time market news in under ten seconds, empowering traders to grasp market shifts instantly and cut through the noise.
AI Business Name Generator
Unlock creativity with our AI Business Name Generator, creating unique and memorable names for startups and brands in seconds.
Opal44
Opal44 gives you plain English AI insights from your website data instantly.
Fusedash
Fusedash transforms raw data into interactive dashboards and charts, enabling teams to act on insights instantly.
finban
Finban is your AI-powered liquidity OS for confident, real-time financial decisions.
HintGo
HintGo uses AI to instantly uncover the why behind every piece of user feedback.
aVenture
Discover emerging startups and VC trends with aVenture's AI-powered platform for institutional-grade research and.
iGPT
iGPT transforms email data into trusted, context-aware insights for seamless AI-driven enterprise workflows.
