Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right tool.

Deeploy
Deeploy is the essential AI governance platform for controlling risk and scaling confidently.
Last updated: March 1, 2026
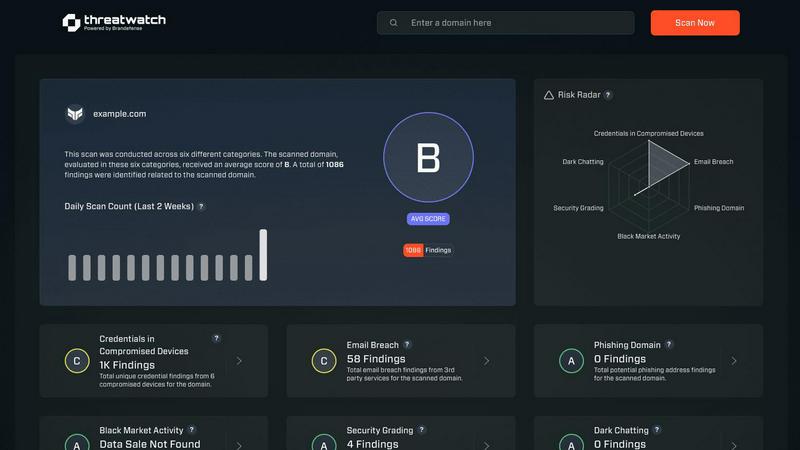
Threat Watch
Instantly evaluate your cybersecurity health and identify vulnerabilities to stay ahead of threats with Threat Watch.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Gain complete visibility across your entire AI landscape with Deeploy's powerful discovery engine. This feature allows you to automatically discover, onboard, and manage every AI system in your organization from a single, unified interface. Connect any MLOps or GenAI platform to eliminate dangerous blind spots and establish centralized control without the need for costly and complex migration projects, ensuring you know exactly what AI is running where.
Control Frameworks
Navigate the complex web of AI regulations with confidence using Deeploy's guided control frameworks. Choose from default, pre-built frameworks like ISO 42001 and NIST AI RMF, or build your own custom set of rules. This feature enables you to classify AI system risk levels in minutes and establish clear accountability with structured approval processes, making compliance straightforward and manageable instead of a manual, error-prone nightmare.
Control Implementation
Turn high-level governance policies into enforceable, engineer-friendly controls. Deeploy automatically assigns the right requirements to every AI system without manual work, giving technical teams clear, actionable tasks. Accelerate compliance by up to 90% using pre-built templates and automatically collected evidence, and let AI-powered assessments handle the repetitive work of validation and documentation.
Real-Time Monitoring
Prevent costly AI incidents before they happen with Deeploy's proactive, real-time monitoring suite. Get instant alerts for critical issues like model drift, performance degradation, or output anomalies. This feature allows you to identify errors before your users do and add essential tracing and guardrails to protect Large Language Model (LLM) outputs, ensuring systems perform as intended and within defined ethical boundaries.
Threat Watch
Comprehensive Security Evaluation
Threat Watch conducts a thorough evaluation across multiple security categories, including compromised credentials and dark web contents, providing users with an expansive view of their cybersecurity health.
Real-Time Insights
Equipped with real-time insights, Threat Watch enables organizations to swiftly identify vulnerabilities and exposures, ensuring that they can act immediately to address potential threats.
Automated Assessments
Streamlining the security process, Threat Watch offers automated assessments that reduce the burden on IT teams, allowing them to focus on strategic initiatives rather than manual monitoring.
Dark Web Monitoring
With robust dark web monitoring capabilities, Threat Watch alerts organizations to compromised data and credentials being traded or sold, helping to prevent identity theft and data breaches.
Use Cases
Deeploy
Financial Services Compliance
For banks and fintechs, Deeploy is the frontline defense against regulatory risk. It provides the immutable audit trails, real-time model monitoring, and explainability required to meet stringent financial regulations. Organizations can prove their credit-scoring or fraud detection models are fair, unbiased, and compliant, scaling AI-driven innovation without exposing the business to massive fines or reputational damage.
Healthcare AI Safety
In sensitive fields like mental and physical healthcare, Deeploy enables the safe adoption of AI. It provides the crucial explainability and expert-in-the-loop feedback mechanisms needed to validate AI-assisted diagnoses or treatment recommendations. This ensures AI augments care responsibly, building patient and practitioner trust while maintaining strict adherence to medical ethics and data privacy standards like HIPAA.
Manufacturing & Supply Chain Optimization
Manufacturers using AI for predictive maintenance, quality control, or supply chain logistics use Deeploy to ensure reliability and traceability. The platform offers observability for both technical and non-technical teams, allowing continuous improvement managers to understand AI reasoning and provide feedback. This turns AI from a black-box tool into a transparent, continuously improving asset integral to production processes.
Enterprise-Wide AI Portfolio Management
Large enterprises with AI scattered across dozens of teams and vendors use Deeploy to regain control. It creates a central registry of all AI assets, applies consistent governance frameworks, and automates evidence collection for audits. This use case transforms AI from an unmanageable jungle into a compliant, high-value portfolio, enabling leadership to scale initiatives with confidence and clear oversight.
Threat Watch
Proactive Risk Management
IT security teams can utilize Threat Watch to proactively manage risks by identifying vulnerabilities before they are exploited, thereby preventing costly data breaches and reputational damage.
Compliance and Regulatory Adherence
Compliance officers can leverage Threat Watch to ensure their organization meets regulatory requirements by continuously monitoring for security gaps and addressing them promptly.
Incident Response
In the event of a security incident, organizations can use Threat Watch to quickly assess the situation, identify compromised accounts, and take immediate action to remediate threats.
Executive Reporting
Business leaders can rely on Threat Watch to provide critical data and insights that facilitate informed decision-making regarding cybersecurity investments and strategies, enhancing overall governance.
Overview
About Deeploy
In the explosive era of enterprise AI, where models are proliferating faster than oversight can keep up, Deeploy emerges as the critical governance infrastructure you can't afford to ignore. This isn't just another monitoring tool; it's a comprehensive AI Governance Operating System designed to bring order to the chaos. As regulations like the EU AI Act set hard compliance deadlines and the risks of ungoverned AI make headlines, Deeploy provides the central nervous system for responsible AI at scale. It's built for organizations—from financial services to healthcare—that are deploying AI across multiple teams and platforms but are losing sleep over blind spots, compliance gaps, and potential model failures. Deeploy's core value proposition is stark: take complete control or be exposed. It transforms a scattered jungle of AI systems into a fully managed, transparent, and compliant portfolio. By offering flexible onboarding, real-time explainability, human feedback loops, and immutable audit trails, Deeploy doesn't just help you meet standards; it builds foundational trust, enabling you to scale AI initiatives faster without the paralyzing fear of operational or regulatory risk. It's the essential layer for any organization running AI at scale, turning governance from a bottleneck into a competitive accelerator.
About Threat Watch
Threat Watch is an advanced cybersecurity intelligence solution tailored to empower organizations in safeguarding their digital assets. Designed for IT security teams, compliance officers, and business leaders, this tool meticulously evaluates a wide range of critical security categories, including compromised credentials, breached accounts, phishing addresses, and dark web contents. With Threat Watch, organizations gain access to real-time insights and automated assessments that enable them to quickly identify vulnerabilities and exposures. This proactive approach to risk management is essential for protecting sensitive data in today's rapidly evolving cyber landscape. By uncovering critical security issues, Threat Watch equips decision-makers with the information needed to prioritize and mitigate risks effectively, ultimately strengthening the overall cybersecurity posture of the organization. Fast and efficient, Threat Watch allows users to uncover their cybersecurity health in record time, thereby enhancing their defenses against potential threats.
Frequently Asked Questions
Deeploy FAQ
What is an AI Governance Operating System?
An AI Governance Operating System is a foundational software layer that manages, monitors, and controls all AI systems across an organization. Deeploy acts as this central nervous system, providing the essential infrastructure for inventory, risk assessment, compliance enforcement, and real-time oversight. It's not just a point tool; it's the integrated platform that makes responsible and scalable AI operation possible.
How does Deeploy help with the EU AI Act compliance?
Deeploy provides guided workflows specifically designed to address the EU AI Act's requirements. It helps you classify AI systems by risk level (unacceptable, high, limited, minimal), implement the corresponding mandatory controls, and automatically generate the necessary documentation and audit trails. This turns the complex act into an actionable, manageable process within your existing AI stack.
Can Deeploy connect to our existing MLOps and AI platforms?
Yes, absolutely. Deeploy is built for flexibility and is designed to connect with any MLOps platform (like MLflow, Kubeflow) or GenAI vendor ecosystem. It discovers and onboards AI systems from these environments without requiring you to migrate or replace your existing tools, providing a governance layer over your heterogeneous AI landscape.
How does the real-time monitoring prevent AI incidents?
Deeploy's monitoring continuously tracks key performance indicators, data drift, and model behavior. It uses configurable alerting to notify teams the moment an anomaly or performance drop is detected—such as a lending model starting to show bias or a chatbot generating harmful content. This allows for proactive intervention before the issue impacts end-users or creates a compliance violation, effectively putting a safety net under production AI.
Threat Watch FAQ
How does Threat Watch identify compromised credentials?
Threat Watch employs advanced algorithms and data analysis techniques to scan for compromised credentials across various platforms and databases, providing users with timely alerts.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your cybersecurity framework without disrupting current operations.
What types of organizations benefit the most from Threat Watch?
Organizations of all sizes, from small businesses to large enterprises, can benefit from Threat Watch, particularly those in sectors with stringent security requirements such as finance, healthcare, and e-commerce.
Is Threat Watch suitable for non-technical users?
Absolutely! Threat Watch is user-friendly and designed with non-technical users in mind, providing intuitive interfaces and detailed reports that make cybersecurity accessible to all levels of staff.
Alternatives
Deeploy Alternatives
Deeploy is a leading AI governance platform, a critical category in the Business Intelligence and MLOps landscape as enterprises scramble to manage AI risk. It functions as a central operating system to control, explain, and audit AI models at scale, ensuring compliance and building trust. Users explore alternatives for various reasons. Some need a solution tailored to a specific tech stack or a lighter-weight tool for smaller deployments. Others may prioritize different pricing models, require niche features Deeploy doesn't emphasize, or seek platforms with a stronger focus on a particular aspect like model performance monitoring over comprehensive governance. When evaluating an alternative, look beyond basic monitoring. The essential checklist includes robust model discovery and registry capabilities, flexible compliance framework support, real-time explainability features, and immutable audit trails for accountability. The right platform should seamlessly integrate with your existing MLOps tools while providing the governance muscle to turn regulatory pressure into a competitive advantage.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence solution that falls under the category of business intelligence. It is designed to help organizations evaluate their cybersecurity health by identifying vulnerabilities and providing actionable insights. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, and compatibility with existing platforms. When selecting an alternative, it’s essential to consider the comprehensiveness of risk analysis, the effectiveness of real-time insights, and the quality of automated assessments to ensure robust cybersecurity management.
