Fusedash vs Threat Watch
Side-by-side comparison to help you choose the right tool.
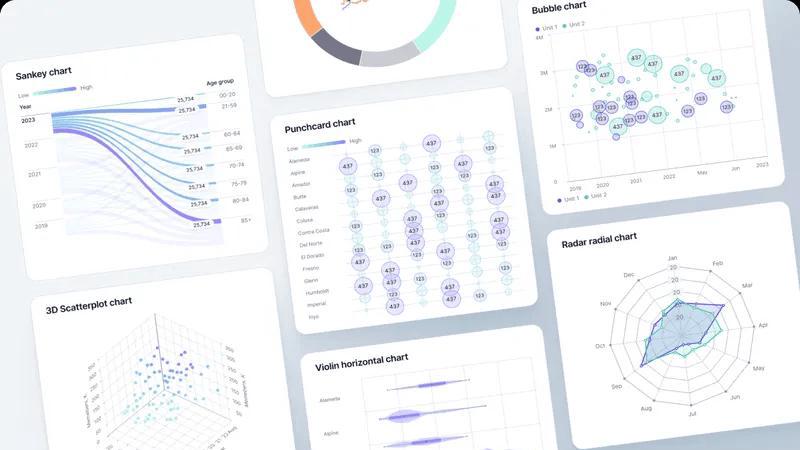
Fusedash transforms raw data into interactive dashboards and charts, enabling teams to act on insights instantly.
Last updated: March 4, 2026
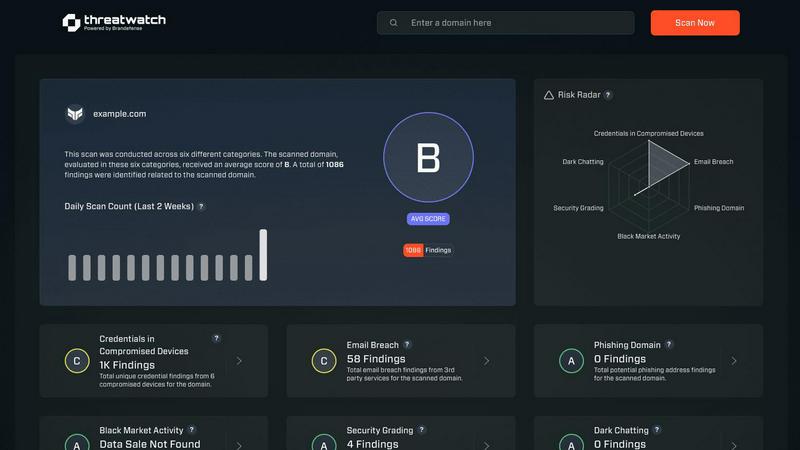
Threat Watch
Instantly evaluate your cybersecurity health and identify vulnerabilities to stay ahead of threats with Threat Watch.
Last updated: March 1, 2026
Visual Comparison
Fusedash
Threat Watch
Feature Comparison
Fusedash
Flexible Views
Fusedash offers the ability to create tailored dashboard views for different audiences. Teams can transform the same dataset into various formats, including dashboards, charts, maps, and report-style views. This customization allows stakeholders to focus on what matters most without the need for lengthy back-and-forth discussions, improving clarity and efficiency.
AI Chart Generator
The AI Chart Generator within Fusedash allows users to create visually appealing and informative charts quickly from CSV files or APIs. This feature enables users to select the most appropriate chart type, apply comparisons, and refine labels, ensuring that each visual effectively communicates the intended story. Charts can be easily integrated into dashboards or used as standalone visuals for reporting purposes.
Dashboard Software
Fusedash provides a comprehensive workspace for building dashboards and reports. This feature allows users to combine performance metrics with narrative insights, providing critical context that explains changes in data. By blending monitoring and storytelling, Fusedash helps teams stay aligned and minimizes the risk of conflicting reports, ensuring everyone is on the same page.
AI Chat
The AI Chat feature enhances user experience by enabling plain language queries about data. Users can ask questions, explore various breakdowns, and receive suggestions for the best metrics and visualizations. This intuitive interaction allows teams to quickly turn insights into shareable dashboard views, making data exploration more accessible and efficient.
Threat Watch
Comprehensive Security Evaluation
Threat Watch conducts a thorough evaluation across multiple security categories, including compromised credentials and dark web contents, providing users with an expansive view of their cybersecurity health.
Real-Time Insights
Equipped with real-time insights, Threat Watch enables organizations to swiftly identify vulnerabilities and exposures, ensuring that they can act immediately to address potential threats.
Automated Assessments
Streamlining the security process, Threat Watch offers automated assessments that reduce the burden on IT teams, allowing them to focus on strategic initiatives rather than manual monitoring.
Dark Web Monitoring
With robust dark web monitoring capabilities, Threat Watch alerts organizations to compromised data and credentials being traded or sold, helping to prevent identity theft and data breaches.
Use Cases
Fusedash
Marketing Analytics
Marketing teams can leverage Fusedash to visualize campaign performance metrics and track KPIs in real-time. By creating tailored dashboards, they can analyze customer engagement, conversion rates, and ROI, enabling data-driven decision-making that optimizes marketing strategies.
Sales Performance Monitoring
Sales teams can utilize Fusedash to monitor their performance metrics and identify trends in sales data. By using interactive dashboards, they can gain insights into sales cycles, customer segmentation, and territory performance, helping them make informed decisions that drive growth.
Financial Reporting
Finance departments can benefit from Fusedash by creating detailed financial reports that incorporate real-time data. With the ability to define consistent metrics, they can ensure accuracy in reporting, analyze trends over time, and present findings to stakeholders with clarity and context.
Operational Efficiency Tracking
Operations teams can use Fusedash to track efficiency metrics and monitor key performance indicators. By visualizing operational data, they can identify bottlenecks, optimize processes, and ensure resources are allocated effectively to enhance overall productivity.
Threat Watch
Proactive Risk Management
IT security teams can utilize Threat Watch to proactively manage risks by identifying vulnerabilities before they are exploited, thereby preventing costly data breaches and reputational damage.
Compliance and Regulatory Adherence
Compliance officers can leverage Threat Watch to ensure their organization meets regulatory requirements by continuously monitoring for security gaps and addressing them promptly.
Incident Response
In the event of a security incident, organizations can use Threat Watch to quickly assess the situation, identify compromised accounts, and take immediate action to remediate threats.
Executive Reporting
Business leaders can rely on Threat Watch to provide critical data and insights that facilitate informed decision-making regarding cybersecurity investments and strategies, enhancing overall governance.
Overview
About Fusedash
Fusedash is an innovative AI-powered data visualization platform that revolutionizes how teams interact with their data. It simplifies the process of transforming connected data into clear, actionable insights by acting as a unified workspace. With Fusedash, users can create decision-ready dashboards, interactive charts, detailed maps, and narrative reports without the hassle of rebuilding logic across multiple disconnected tools. The platform is designed for teams that are tired of manual reporting cycles and conflicting data narratives. By defining key metrics and KPIs once, Fusedash ensures that every team member—from leadership to marketing to operations—works with the same trusted numbers. This consistency not only enhances efficiency but also fosters alignment across the organization. Fusedash empowers users to monitor real-time data while providing insights into the reasons behind trends through advanced drill-down capabilities. With integrated AI features, such as natural language data chat and smart visualization assistance, Fusedash makes data exploration and reporting faster and more accessible, turning raw data into a shared source of truth that drives informed decision-making and strategic action.
About Threat Watch
Threat Watch is an advanced cybersecurity intelligence solution tailored to empower organizations in safeguarding their digital assets. Designed for IT security teams, compliance officers, and business leaders, this tool meticulously evaluates a wide range of critical security categories, including compromised credentials, breached accounts, phishing addresses, and dark web contents. With Threat Watch, organizations gain access to real-time insights and automated assessments that enable them to quickly identify vulnerabilities and exposures. This proactive approach to risk management is essential for protecting sensitive data in today's rapidly evolving cyber landscape. By uncovering critical security issues, Threat Watch equips decision-makers with the information needed to prioritize and mitigate risks effectively, ultimately strengthening the overall cybersecurity posture of the organization. Fast and efficient, Threat Watch allows users to uncover their cybersecurity health in record time, thereby enhancing their defenses against potential threats.
Frequently Asked Questions
Fusedash FAQ
What types of data can I connect to Fusedash?
Fusedash supports a wide range of data sources, including CSV files, APIs, and public datasets. This flexibility allows users to consolidate various data points into a single platform for comprehensive analysis and reporting.
How does Fusedash ensure consistency in reporting?
Fusedash enables users to define key metrics and KPIs only once, which can then be reused across all dashboards, charts, and reports. This standardization ensures that every team member is viewing the same trusted data, reducing discrepancies and conflicting reports.
Can I customize the visualizations in Fusedash?
Yes, Fusedash offers extensive customization options for visualizations. Users can adjust layouts, filters, and time ranges, allowing them to tailor the data views to meet the specific needs of different stakeholders and audiences.
Is Fusedash suitable for teams with varying data expertise?
Absolutely. Fusedash is designed for users of all skill levels. With its intuitive interface and AI-powered features, even those with limited data expertise can easily navigate the platform, ask questions, and generate insightful reports.
Threat Watch FAQ
How does Threat Watch identify compromised credentials?
Threat Watch employs advanced algorithms and data analysis techniques to scan for compromised credentials across various platforms and databases, providing users with timely alerts.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your cybersecurity framework without disrupting current operations.
What types of organizations benefit the most from Threat Watch?
Organizations of all sizes, from small businesses to large enterprises, can benefit from Threat Watch, particularly those in sectors with stringent security requirements such as finance, healthcare, and e-commerce.
Is Threat Watch suitable for non-technical users?
Absolutely! Threat Watch is user-friendly and designed with non-technical users in mind, providing intuitive interfaces and detailed reports that make cybersecurity accessible to all levels of staff.
Alternatives
Fusedash Alternatives
Fusedash is an advanced AI-powered data visualization platform that enables teams to transform their raw data into clear, actionable insights through decision-ready dashboards, interactive charts, and detailed reports. As part of the Analytics & Data and Business Intelligence categories, Fusedash simplifies data exploration and reporting, making it a vital tool for organizations looking to align their teams around trusted metrics. Users often seek alternatives to Fusedash for various reasons, including pricing, specific feature sets, or particular platform needs that better fit their operational requirements. When considering alternatives, it's essential to evaluate the platform's usability, integration capabilities, support options, and the flexibility to customize dashboards and reports. A solid alternative should also provide an intuitive interface and ensure consistency in data reporting across all departments.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence solution that falls under the category of business intelligence. It is designed to help organizations evaluate their cybersecurity health by identifying vulnerabilities and providing actionable insights. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, and compatibility with existing platforms. When selecting an alternative, it’s essential to consider the comprehensiveness of risk analysis, the effectiveness of real-time insights, and the quality of automated assessments to ensure robust cybersecurity management.
