iGPT vs Threat Watch
Side-by-side comparison to help you choose the right tool.
iGPT transforms email data into trusted, context-aware insights for seamless AI-driven enterprise workflows.
Last updated: March 1, 2026
Threat Watch
Instantly evaluate your cybersecurity health and identify vulnerabilities to stay ahead of threats with Threat Watch.
Last updated: March 1, 2026
Visual Comparison
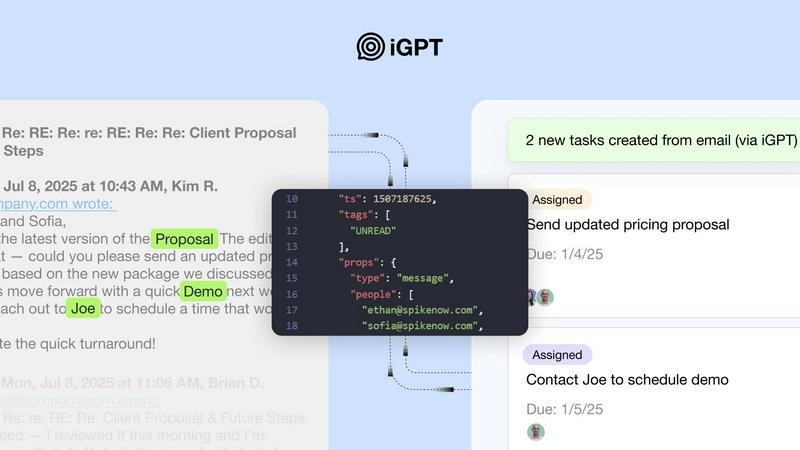
iGPT
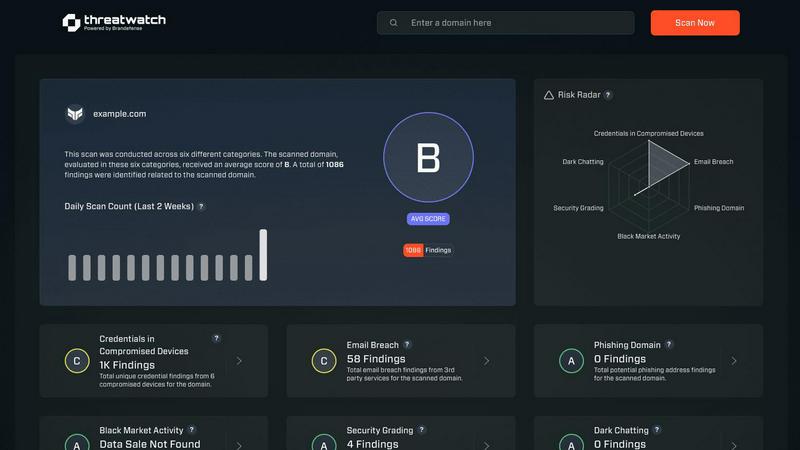
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT provides a seamless SDK and live playground that allows developers to test requests and responses quickly. This immediate integration facilitates a faster deployment process, enabling teams to harness the power of email intelligence without the typical delays associated with onboarding.
Contextual Responses
With iGPT, the responses generated are not just raw data but are context-aware and ready for reasoning and automation. Each response is accompanied by citations to the original source, providing clarity and accountability, which are essential for any enterprise-level application.
Hybrid Retrieval
The hybrid retrieval feature combines semantic and keyword searches, along with customizable filters. This allows users to retrieve the most relevant information from vast email datasets, scored and reranked in a single API call, thus eliminating the need for multiple queries.
Continuous Data Indexing
iGPT ensures that data stays up-to-date through continuous live indexing. New messages and attachments are indexed instantly, meaning that users always have access to the latest information, enhancing decision-making efficiency and accuracy.
Threat Watch
Comprehensive Security Evaluation
Threat Watch conducts a thorough evaluation across multiple security categories, including compromised credentials and dark web contents, providing users with an expansive view of their cybersecurity health.
Real-Time Insights
Equipped with real-time insights, Threat Watch enables organizations to swiftly identify vulnerabilities and exposures, ensuring that they can act immediately to address potential threats.
Automated Assessments
Streamlining the security process, Threat Watch offers automated assessments that reduce the burden on IT teams, allowing them to focus on strategic initiatives rather than manual monitoring.
Dark Web Monitoring
With robust dark web monitoring capabilities, Threat Watch alerts organizations to compromised data and credentials being traded or sold, helping to prevent identity theft and data breaches.
Use Cases
iGPT
Email Assistants
iGPT can be leveraged to build intelligent agents that draft, prioritize, and act on emails, providing full context around each interaction. This streamlines workflows and enhances productivity, allowing users to focus on higher-value tasks.
Workflow Automation
Organizations can harness iGPT to turn lengthy email threads into actionable tasks, deadlines, and approvals. This automation minimizes the risk of tasks falling through the cracks and ensures that critical activities are flagged and addressed promptly.
Support Copilots
Support teams can utilize iGPT to reconstruct comprehensive customer stories from extended email chains. By analyzing attachments and tone shifts, support agents can deliver personalized and contextually relevant responses, improving customer satisfaction.
Compliance and Audit Trail
iGPT enhances compliance monitoring by providing a full audit trail of conversations. This feature allows organizations to trace feedback, approvals, and rationale back to original emails, ensuring transparency and accountability in decision-making processes.
Threat Watch
Proactive Risk Management
IT security teams can utilize Threat Watch to proactively manage risks by identifying vulnerabilities before they are exploited, thereby preventing costly data breaches and reputational damage.
Compliance and Regulatory Adherence
Compliance officers can leverage Threat Watch to ensure their organization meets regulatory requirements by continuously monitoring for security gaps and addressing them promptly.
Incident Response
In the event of a security incident, organizations can use Threat Watch to quickly assess the situation, identify compromised accounts, and take immediate action to remediate threats.
Executive Reporting
Business leaders can rely on Threat Watch to provide critical data and insights that facilitate informed decision-making regarding cybersecurity investments and strategies, enhancing overall governance.
Overview
About iGPT
In the rapidly evolving landscape of artificial intelligence, email remains a critical yet often overlooked data source. Enter iGPT, the game-changing enterprise-grade API that revolutionizes how organizations access and utilize email and communication data. Designed for engineers and enterprises alike, iGPT transforms the chaotic nature of email conversations and attachments into structured, actionable intelligence. This platform is a secure and auditable gateway specifically tailored for the next generation of AI systems, enabling them to grasp context rather than merely keywords. By offering a single unified endpoint, iGPT streamlines the entire complex pipeline—from real-time data ingestion to hybrid retrieval and context shaping—allowing engineering teams to sidestep extensive infrastructure development. Built with security-first enterprises in mind, iGPT ensures zero data training, comprehensive audit trails, and flexible deployment options, making compliance and trust paramount. Whether you are developing sales copilots, deal intelligence systems, or automated compliance agents, iGPT stands as the mission-critical layer that transforms the disarray of communication into your most formidable competitive advantage.
About Threat Watch
Threat Watch is an advanced cybersecurity intelligence solution tailored to empower organizations in safeguarding their digital assets. Designed for IT security teams, compliance officers, and business leaders, this tool meticulously evaluates a wide range of critical security categories, including compromised credentials, breached accounts, phishing addresses, and dark web contents. With Threat Watch, organizations gain access to real-time insights and automated assessments that enable them to quickly identify vulnerabilities and exposures. This proactive approach to risk management is essential for protecting sensitive data in today's rapidly evolving cyber landscape. By uncovering critical security issues, Threat Watch equips decision-makers with the information needed to prioritize and mitigate risks effectively, ultimately strengthening the overall cybersecurity posture of the organization. Fast and efficient, Threat Watch allows users to uncover their cybersecurity health in record time, thereby enhancing their defenses against potential threats.
Frequently Asked Questions
iGPT FAQ
What makes iGPT different from other email retrieval tools?
iGPT is not merely a retrieval tool; it is an enterprise-grade API designed to provide structured, context-aware intelligence from emails. Its ability to process attachments and deliver contextual responses sets it apart from conventional solutions.
How does iGPT ensure data security?
iGPT employs a security-first approach, featuring zero data retention, role-based access control (RBAC), and no data training. This ensures that your data remains confidential and under your control at all times.
Can iGPT integrate with existing systems?
Yes, iGPT is designed for immediate integration with existing systems through its SDK and unified endpoint. This allows organizations to implement email intelligence without extensive infrastructure changes.
What types of organizations can benefit from using iGPT?
iGPT is suitable for a wide range of organizations, particularly those that rely heavily on email communication. This includes sales teams, customer support, compliance departments, and any enterprise looking to enhance its workflow automation and intelligence capabilities.
Threat Watch FAQ
How does Threat Watch identify compromised credentials?
Threat Watch employs advanced algorithms and data analysis techniques to scan for compromised credentials across various platforms and databases, providing users with timely alerts.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your cybersecurity framework without disrupting current operations.
What types of organizations benefit the most from Threat Watch?
Organizations of all sizes, from small businesses to large enterprises, can benefit from Threat Watch, particularly those in sectors with stringent security requirements such as finance, healthcare, and e-commerce.
Is Threat Watch suitable for non-technical users?
Absolutely! Threat Watch is user-friendly and designed with non-technical users in mind, providing intuitive interfaces and detailed reports that make cybersecurity accessible to all levels of staff.
Alternatives
iGPT Alternatives
iGPT is an advanced API solution designed specifically for enterprises seeking to harness the power of email data for AI-driven applications. Positioned within the business intelligence category, it transforms unstructured email communications into structured, actionable insights, allowing AI agents to operate with contextual intelligence. Users often seek alternatives to iGPT for various reasons, including pricing considerations, feature sets, integration capabilities, or specific platform requirements that may not align with their operational needs. When exploring alternatives, it’s crucial to evaluate factors such as ease of integration, the ability to handle complex data pipelines, security features, and the overall user experience. Selecting an option that offers robust data processing capabilities and a reliable support system can significantly impact the effectiveness of your AI applications.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence solution that falls under the category of business intelligence. It is designed to help organizations evaluate their cybersecurity health by identifying vulnerabilities and providing actionable insights. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, and compatibility with existing platforms. When selecting an alternative, it’s essential to consider the comprehensiveness of risk analysis, the effectiveness of real-time insights, and the quality of automated assessments to ensure robust cybersecurity management.
